Unfortunately, many people don’t realize that re-using passwords is kind of like using the same key for your house, car, safety deposit box, gym locker and bike lock, and then sharing that key with a number of people you don’t really know. Even if those people seem trustworthy, a few of them might not take the same steps to protect that key. They might even put your name and address on it and leave it in plain sight for their own convenience… to keep track of who’s keys they are borrowing.
When you re-use a password on a new website, you are essentially sharing your key with a person (or number of people) that you don’t really know. Unlike a physical key that protects your physical possessions, passwords protect your online identity. In the wrong hands, they can be used to steal your identity, whether they break into your accounts and steal directly from you, or create false accounts to “borrow” money or buy things in your name, things that people will expect you to re-pay. Unlike a physical key, many hackers from many different countries can steal and create copies of your login information without you knowing it (there is no hint that someone stole it.. unlike a physical key where you would at least notice if it was “missing”).
Hackers know that many people re-use passwords. When they break into a website with little or no security, they will use the emails and passwords they find and attempt to access other websites with those same credentials. If you don’t re-use passwords, congratulations, you may have just saved your online identity and prevented a lot of pain and suffering.
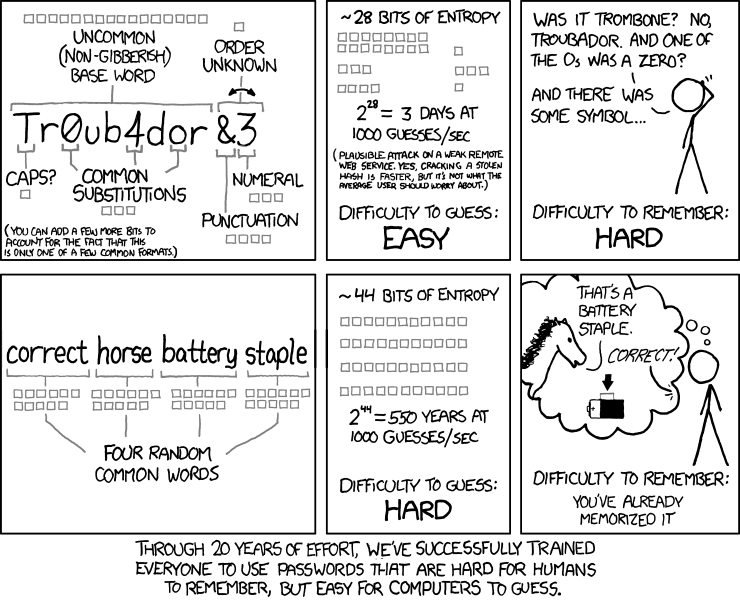
Now that I convinced you to start using different passwords for different websites, let me include a comic I found that will help you come up with easy to remember, hard to crack passwords:
If you manage or develop a website, see this related article: Protecting User Accounts – Password Management